I will try to elaborate the cryptographity technology called Zero-Knowledge Proofs which is one of the most powerful techonolgies that are reshaping how privacy and security work online in this article.
- What Are Zero-Knowledge Proofs?
- Why Zero-Knowledge Proofs Matter Today
- Stronger Digital Privacy
- Protection Against Data Breaches
- Trust Without Sharing Secrets
- Safer Online Authentication
- Enhanced Blockchain Security
- Compliance With Privacy Regulations
- Future of Digital Identity
- How Zero-Knowledge Proofs Work
- The Prover Makes a Claim
- Mathematical Challenge is Created
- Proof Without Disclosure
- Verification Process
- Repeated or Non-Interactive Proofs
- Result: Trust Through Mathematics
- Benefits of Zero-Knowledge Proof Technology
- Enhanced Data Privacy
- Stronger Security
- Passwordless Authentication
- Reduced Data Storage Requirements
- Improved Blockchain Scalability
- Trust Without Intermediaries
- Regulatory Compliance Support
- Zero-Knowledge Proofs in Cryptocurrency & Blockchain
- Types of Zero-Knowledge Proofs
- Interactive Zero-Knowledge Proofs
- Non-Interactive Zero-Knowledge Proofs (NIZKs)
- zk-SNARKs* (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge)
- Bulletproofs
- zk-Rollups
- Recursive Zero-Knowledge Proofs
- Transparent Zero-Knowledge Proofs
- Real-World Applications Beyond Crypto
- Secure Passwordless Login
- Digital Identity Verification
- Online Voting Systems
- Healthcare Data Protection
- Financial Compliance (KYC & AML)
- Supply Chain Verification
- Secure Cloud Computing
- Academic Credential Verification
- Challenges and Limitations
- Technical Complexity
- High Computational Requirements
- Expensive Development Costs
- Limited Developer Knowledge
- Trusted Setup Concerns
- Scalability Trade-offs
- Regulatory Uncertainty
- The Future of Zero-Knowledge Proofs
- Conclusion
- FAQ
Zero-Knowledge Proofs provide safety in digital information exchange where data can be verified without divulging sensitive private info. Blockchain has opened up new avenues from innovation to secure authentication systems that define the future of privacy-oriented internet apps and digital trust over generations.
What Are Zero-Knowledge Proofs?
Zero-Knowledge Proofs (ZKPs) are encrypted methods, a cryptographic protocol where one party can prove to another that they know something is true without revealing the underlying information. A user can prove the ownership or authenticity of sensitive data without actually sharing information such as passwords, identity details or financial records publicly; Instead mathematically.
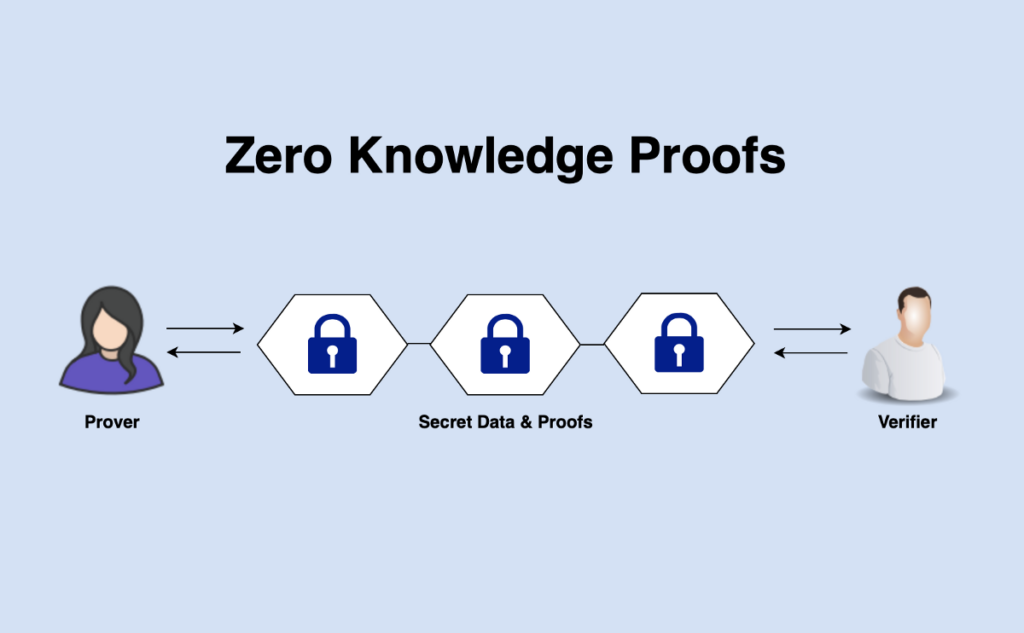
It is based on the paradigm of zero-knowledge proofs where a “prover” convinces another party — i.e., a verifier, without revealing himher-secrets. ZKPs have their own advantages as they improve security, reduce data leaks and enable trust in digital systems.
They find applications in, among many others: blockchain technology, secure authentication systems, privacy-focused applications and the next-generation internet protocols focusing on user data protection.
Why Zero-Knowledge Proofs Matter Today
Stronger Digital Privacy
Zero-Knowledge Proofs enable users to see if the information is true, without having access. With privacy now a commodity in the preventative shelf life, this tech helps mask identities, passwords and sensitive information from bot-uses.
Protection Against Data Breaches
Being large repositories of user data, traditional systems are a major target for hackers. They provide ZKPs, which minimizes information stored → in most scenarios even if systems are attacked there is little that a bad actor can extract.
Trust Without Sharing Secrets
ZKPs enable verification without exposure. Without exposing private information, businesses and governments—and secondarily online platforms—are able to verify that someone is eligible for something or own an asset or ID.
Safer Online Authentication
Zero-Knowledge systems use logins without passwords which can be stolen–the system allows users to prove they have access rights, but the login cannot prove who you are.
Enhanced Blockchain Security
ZKPs are used by blockchain networks (such as zk-SNARK) to verify transactions without revealing the transaction data, thus enhancing scalability and confidentiality while maintaining system transparency and security.
Compliance With Privacy Regulations
As global privacy laws continue to rise, compliance requirements can be validated without putting customer data at risk while minimizing legal and operational risks.
Future of Digital Identity
ZKPs enable self-sovereign identity systems, where users control their data and provide proof of what’s necessary instead of full records.
How Zero-Knowledge Proofs Work
The Prover Makes a Claim
The prover asserts they have information, such as a password, correct funds ownership or legitimate credentials for access but discloses no data.
Mathematical Challenge is Created
A cryptographic challenge sent by the verifier The challenge must be answered correctly, and this can only occur if the prover actually knows some secret information.
Proof Without Disclosure
The response from the prover involves advanced cryptographic computations. It gives a correct response but hides the raw data entirely.
Verification Process
The check performed by the verifier to establish correctness of a mathematical proof using public rules or algorithms. To explain, the verifier accepts or declines a claim based on whether it is true without knowing anything about what secret has been proven.
Repeated or Non-Interactive Proofs
The proof can be interactive for many rounds or then the proofs could also become a non-interactive single proof about which immediate verification is possible without further communication whatsoever.
Result: Trust Through Mathematics
Zero-Knowledge Proofs do not rely on people or institutions to create trust, it uses cryptography to establish a trusted process for secure authentication, private transactions and validation of information regarding the assets.
Benefits of Zero-Knowledge Proof Technology

Enhanced Data Privacy
Private computations powered by Zero-Knowledge Proofs (ZKPs) help users prove their facts without transmitting any sensitive information and this also ensures that the private data is kept confidential, safe from all unauthorized access.
Stronger Security
There is almost no risk of hacking, identity theft and data breaches when private information is never shared or stored openly.
Passwordless Authentication
The ZKP systems help people log in safely and securely without passwords which reduces risks associated with password leaks, phishing attacks, and credential theft.
Reduced Data Storage Requirements
Also traditional cloud services do not require massive data storage where your data will be stored in plain text.
Improved Blockchain Scalability
This technology allows distinguishing the relevant data from non-essential ones by processing them without exposing their details. This, in turn, helps speed up blockchain networks transaction verification process.
Trust Without Intermediaries
It allows users to prove ownership, identity or eligibility with cryptographic proofs directly and less on a centralized authority or third parties.
Regulatory Compliance Support
This is useful to show that businesses are in compliance with any and all applicable regulations, while still not revealing potentially sensitive data about customers or firms, assisting companies meet their privacy and legal requirements.
Zero-Knowledge Proofs in Cryptocurrency & Blockchain
| Use Case | How ZK Proofs Are Used | Benefits | Example Blockchain |
|---|---|---|---|
| Private Transactions | Transaction details are verified without revealing sender, receiver, or amount. | Financial privacy while maintaining blockchain validation. | Zcash |
| Blockchain Scaling (Layer-2) | Thousands of transactions are bundled into one proof and verified on the main chain. | Faster transactions and lower fees. | Polygon |
| zk-Rollups | Multiple off-chain transactions generate a single cryptographic proof submitted on-chain. | Improved scalability and reduced network congestion. | StarkNet |
| Privacy Smart Contracts | Smart contracts execute logic without exposing sensitive user data publicly. | Confidential decentralized applications. | Ethereum |
| Identity Verification | Users prove eligibility or identity without sharing personal information. | Secure digital identity and compliance-friendly verification. | Web3 identity protocols |
| Exchange Proof of Reserves | Crypto exchanges prove they hold funds without exposing wallet balances. | Increased transparency and user trust. | Centralized & decentralized exchanges |
| Cross-Chain Verification | Proofs validate data across multiple blockchains without sharing full datasets. | Better interoperability between networks. | Multi-chain ecosystems |
| Confidential Voting & Governance | Votes are validated without revealing voter identity or choice. | Secure decentralized governance systems. | DAO governance platforms |
Types of Zero-Knowledge Proofs
Interactive Zero-Knowledge Proofs
These are proofs where the prover and verifier have to keep on exchanging messages. The verifier issues several challenges that the prover responds to with confirmations of knowing the secret without revealing it. They are very secure but not the most practical for larger or automated systems.
Non-Interactive Zero-Knowledge Proofs (NIZKs)
This approach involves the prover creating a single proof that is reliant only on prior interaction. This expedites verification and is great for blockchain networks that can not afford constant communication.
zk-SNARKs* (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge)
It generates a very small proof and with which we can verify them, it is called zk-SNARKS. They are lightweight in computation during the verification process and used widely among privacyh sensitive cryptocurrencies or scalable blockchain systems.
Bulletproofs
Bulletproofs are short zero-knowledge proofs (ZKPs) mostly suited for confidential transactions. They are succinct, do not require trusted setup and offer common good privacy guarantees.
zk-Rollups
While a technically simple application of ZK proofs, zk-rollups combine thousands of off-chain transactions into one proof written on chain. Such improvements have a huge impact on speed and transaction fees.
Recursive Zero-Knowledge Proofs
Recursive proofs are the ability for one proof to validate another proof. This allows the existence of continuously verifiable chains, leading to a better scalability and efficiency for complex blockchain and computation systems [3].
Transparent Zero-Knowledge Proofs
They do not require hidden parameters from which the model extracts knowledge; they furthermore avoid trusted initialization phases that would also increase security and decentralization by risk of disputable trust.
Real-World Applications Beyond Crypto
Secure Passwordless Login
Zero-Knowledge Proofs allow for users to verify accounts without ever exposing passwords. As such, platforms are safely able to perform mathematical identity verification and eliminate risks associated with phishing attacks and leaking or buying credentials.
Digital Identity Verification
People get to prove either how old they are (or that they belong to a country), or whether they’re otherwise entitled, just without ever revealing full identity documents. It applies to privacy-centric digital IDs and self-sovereign identity architectures.
Online Voting Systems
With the use of Zero-Knowledge Technology, it is now possible to verify that votes are valid without ever revealing who voted or their choice in particular — a solution for transparency and election security.
Healthcare Data Protection
Patients can prove they are covered by insurance or eligible for medical care without opening entire healthcare records, safeguarding sensitive health information but allowing authorized verification.
Financial Compliance (KYC & AML)
That is, banks and fintechs would be able to verify compliance with the regulatory rules—for instance identity verification via Know Your Customer methods—without having to keep sensitive personal financial data or exposing it.
Supply Chain Verification
Companies are able to proved product authenticity or standards related sourcing and manufacturing with no disclosure of proprietary information surrounding those products.
Secure Cloud Computing
Users can offload data processing to cloud servers with the pri-vacy guarantee of raw file ownership or computation correctness without revealing actual files.
Academic Credential Verification
Students are able to VERIFY degrees, certifications or qualifications without the need of sharing a full transcript/complete records on themselves preventing credential fraud.
Challenges and Limitations
Technical Complexity
Zero-Knowledge Proof (ZKP) systems that use complex cryptography and mathematics, hence making it difficult for developers/organizations to understand, implement and deploy.
High Computational Requirements
In privy and other ZK platforms, generating these clones can take considerable computing power and processing time (especially for larger datasets or more complex applications).
Expensive Development Costs
Developing ZK-based applications also requires dedicated expertise and infrastructure, raising both development and operational costs.
Limited Developer Knowledge
Currently, there are few skilled engineers with experience in zero-knowledge cryptography so broader adoption is still slow to develop.
Trusted Setup Concerns
Some ZK systems have an initial trusted setup phase. The security of the entire system could be compromised if this setup was hacked.
Scalability Trade-offs
ZKPs make verification fast, but generating these proofs is still expensive and this can hamper the performance of various use cases.
Regulatory Uncertainty
Privacy-enhancing technologies can be problematic for regulators since fully private transactions make it harder to monitor potential fraud or illegal activity all the time.
The Future of Zero-Knowledge Proofs

The future of Zero-Knowledge Proofs is woven into the fabric of evolving a digital world that prioritises privacy. With data breaches, surveillance concerns and identity theft only getting worse we expect ZK technology to be a cornerstone of the next generation internet commonly referred to as Web3.
It will also enable secure digital identities, passwordless authentication, private financial transactions and scalable blockchain systems. ZK solutions provide the ability to verify information without revealing sensitive data which are compelling for enterprises, governments and AI platforms alike.
Over the next few years, Zero-Knowledge Proofs could change how everyone will interact online by replacing our trust in institutions with a kind of mathematics — cryptographic verification.
Conclusion
To step back from the crypto world for a moment, zero-knowledge proofs are one of those rare and monumental innovations that is massively powerful but frequently undervalued. They address major challenge of net, how to build trust without revealing information itself as you enable this info on data can be validated without exposing it.
Working well from healthcare, finance, cryptocurrency and even digital identity to the recently acquired secure online authentication ZK is driving how systems store this sensitive information.
While challenges around complexity and availability still exist, the upside is vast. With the digital world heading towards privacy-first solutions, Zero-Knowledge Proofs will continue to be an essential component for secure, transparent and user-oriented relationships.
FAQ
What is a Zero-Knowledge Proof in simple terms?
A Zero-Knowledge Proof is a cryptographic method that allows someone to prove a statement is true without revealing the actual information behind it. It confirms validity while keeping data completely private.
Why are Zero-Knowledge Proofs important?
They improve digital privacy and security by reducing the need to share sensitive data such as passwords, financial details, or personal identity information.
Where are Zero-Knowledge Proofs used today?
ZKPs are widely used in blockchain technology, cryptocurrency transactions, secure authentication systems, digital identity solutions, online voting, and data protection applications.
Are Zero-Knowledge Proofs safe?
Yes. When properly implemented, they rely on advanced cryptographic mathematics that makes it extremely difficult for attackers to fake proofs or access hidden information.






