This article will cover Ways to Use zk-Identity to Prove You’re Human Online. zk-Identity uses zero-knowledge proofs to enable verification of human interactions without disclosing private information.
- What is zk-Identity?
- Why Ways to Use zk-Identity to Prove You’re Human Online
- Key Point & Ways to Use zk-Identity to Prove You’re Human Online
- 1. zk‑Biometric Proofs
- zk-Biometric Proofs Features, Pros & Cons
- 2. zk‑Device Attestation
- zk-Device Attestation Features, Pros & Cons
- 3. zk‑Social Graph Proofs
- zk-Social Graph Proofs Features, Pros & Cons
- 4. zk‑Email Ownership
- zk‑Email Ownership Features, Pros & Cons
- 5. zk‑Phone Number Proofs
- zk-Phone Number Proofs Features, Pros & Cons
- 6. zk‑Government ID Proofs
- zk-Government ID Proofs Features, Pros & Cons
- 7. zk‑Age Verification
- zk‑Age Verification Features, Pros & Cons
- 8. zk‑Payment Proofs
- zk‑Payment Proofs Features, Pros & Cons
- 9. zk‑Residency Proofs
- zk‑Residency Proofs Features, Pros & Cons
- 10. zk‑Session Activity Proofs
- zk-Session Activity Proofs Features, Pros & Cons
- Conclusion
- FAQ
The methods include biometrics and device attestation, social, email, and gov ID. These methods of online interaction are private, secure, and fraud-free while also keeping sensitive information hidden, and obfuscating bots and fake accounts.
What is zk-Identity?
A zk-Identity digital identity system gives the user a way to keep their identity a secret by using a zero knowledge privacy system for age, place of residence, and account ownership verification, among other attributes.
Fraud, data privacy breaches, identity theft, and other privacy risks created by traditional identity systems are reduced with zk-Identity systems because they allow companies to confirm a user’s identity while keeping sensitive data secret.
zk-Identity systems can be used online for age verification, for completing tasks that require a government-issued ID, for services that require a credential check, and for social and financial activity verification.
The privacy, security, and simplicity that zk-Identity systems add to digital interactions fosters increased confidence in digital transactions.
Why Ways to Use zk-Identity to Prove You’re Human Online
Verification Without Loss of Privacy – With zk-Identity, the platform can verify that a user is a human without leaking their biometric, email, phone, or any government issued identification.
Disruption of Bots and Spam – By implementing zk-Biometric Proofs, zk-Device Attestation, or zk-Social Graph Proofs, platforms can prevent automated bots and fake accounts and spam.
Safe Access to Services – With zk-Identity, users can access online services, age-restricted content, financial services, or premium apps without any doubts that the user is real.
Regulatory Requirements without Data Exposure – The compliance of a platform to the law is proven with zk-Government ID, zk-Age Verification, or zk-Residency while the user’s data remains private.
Improved Trust and Reputation – Verified users with zk-Identity create a trustworthy online community while zk-Identity significantly decreases fraud and account abuse on the platforms.
Key Point & Ways to Use zk-Identity to Prove You’re Human Online
| zk-Identity Proof | Key Point |
|---|---|
| zk‑Biometric Proofs | Verify human identity using biometric data without revealing sensitive details. |
| zk‑Device Attestation | Confirm the authenticity of a device while keeping user-specific data private. |
| zk‑Social Graph Proofs | Prove social connections or reputation without exposing individual relationships. |
| zk‑Email Ownership | Validate email control without revealing the actual email address. |
| zk‑Phone Number Proofs | Confirm ownership of a phone number while maintaining privacy. |
| zk‑Government ID Proofs | Verify government-issued IDs without sharing the full ID details. |
| zk‑Age Verification | Prove age eligibility without disclosing exact birth date. |
| zk‑Payment Proofs | Demonstrate payment history or transactions without revealing amounts or counterparties. |
| zk‑Residency Proofs | Verify country or city residency without exposing full address. |
| zk‑Session Activity Proofs | Prove online session actions occurred without revealing personal activity details. |
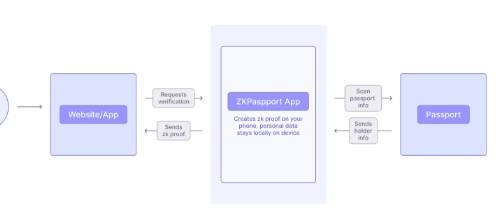
1. zk‑Biometric Proofs
With zk-Biometric proofs, users can be verified as human through biometric methods such as fingerprinting, facial recognition, and iris scans, without revealing the actual biometric data. They can provide verification through the use of zero-knowledge cryptography, which allows users to be verified as real without disclosing private data.
Some online human verification methods using zk-Identity can be used for logging into accounts, accessing private services, and mitigating bot activity on social media. With zk-Biometric proofs, platforms balance privacy and identity verification, increasing the risk of service theft.
zk-Biometric Proofs Features, Pros & Cons
Features:
- Biometric methods include fingerprint, facial, and iris scan.
- Privacy is maintained through zero-knowledge verification.
- Confirms the identity of a human.
- Prevents bot or fake accounts.
- Biometric-enabled device support is available.
Pros:
- Excellent anti-bot capability.
- Provide a high level of reliability and precision.
- Sensitive biometric information is securely stored.
- Provides a good user experience.
- Most recent devices support it.
Cons:
- Biometric devices are a necessity.
- Some users may find it hard to access.
- Dependence of devices.
- Support is limited to a few devices.
- Can be spoofed by a poor anti-bot system.
2. zk‑Device Attestation
Proof of zk-Device Attestation can verify that a legitimate device is being used to access a service without revealing device-specific information, such as the device’s serial number or IP address.
This method can be used to verify that a human as opposed to a bot or automated script is interacting with a platform, and can provide online human verification to protect access, enable the use of certain software, or protect the integrity of user activity on the platform.
This method allows platforms to trust devices while safeguarding user privacy, and provides an improved level of protection and ease of use in the digital service ecosystem.
zk-Device Attestation Features, Pros & Cons
Features:
- Confirms the authenticity of devices.
- Based on zero-knowledge proofs.
- Detects automated or bot-driven logins.
- Works on a silent background.
- Multi-device verification is supported.
Pros:
- Excellent anti-bot capability.
- Protects the privacy of the user.
- Provides a good user experience.
- Improves the security of the system.
- Provides secure device authentication.
Cons:
- May fail to work on a virtual machine.
- Device compatibility issues.
- Limited system support across devices.
- Legitimate users may be blocked by the system.
- System integration on the platform is required.
3. zk‑Social Graph Proofs
A zk-Social Graph Proof provides verification of a user’s online social network while protecting the privacy of their individual social relationships. By employing zero-knowledge proofs, online social platforms can validate social engagement and social trust without revealing social connections.
Examples of uses of zk-Identity proving online humanity include participation in online social communities, access to content behind social community paywalls, and the receipt of social community incentives. This approach decreases the incidence of spam and inauthentic user accounts, while protecting user privacy, and enables online social platforms to ensure trust and authenticity by protecting social privacy.
zk-Social Graph Proofs Features, Pros & Cons
Features:
- Social connections are validated.
- Data privacy is maintained through zero-knowledge verification.
- Measures trust or reputation.
- Reduces spam or fake accounts.
- Community-based verification is supported.
Pros:
- Provides privacy to the social links.
- Improves trust of the platform.
- Provides excellent detection of fake users.
- Works in decentralized networks.
- Human-only verification is supported.
Cons:
- Requires users to have a social presence.
- Complex implementation.
- Adoption is limited.
- Undetectable bots.
- Dependant upon the social data accuracy.
4. zk‑Email Ownership
zk-Email Ownership allows users to verify their control of an email account without disclosing the actual email address. Zero-knowledge cryptography allows platforms to verify a person’s identity by email account control verification while protecting privacy.
Examples of uses of zk-Identity to prove online humanity include account registration, credential recovery, and identity verification for secure communication. This allows email verification to remain effective against bots and anti-fraud systems while protecting user privacy. This allows a user to access online systems safely and anonymously.
zk‑Email Ownership Features, Pros & Cons
Features:
- Establishes a control over an email account.
- Privacy is inherently maintained via zero-knowledge proof.
- Enables account recovery and registration.
- Disposable emails are not permitted.
- The real email is never revealed.
Pros:
- Simple to integrate.
- Email Privacy is maintained.
- Account Security is enhanced.
- Works with all social platforms.
- Bot accounts are reduces.
Cons:
- Anti-bot measures are limited if disposable emails are used.
- Email access is required.
- Identity verification is not possible.
- Platform integration is required.
- Complex email systems may not work.
5. zk‑Phone Number Proofs
With zk-Phone number proofs, users can prove they own a phone number, but do not have to share that number. Platforms can show that a human is interacting with their platform and still keep personal details private. Some examples of using zk-Identity to prove you’re a human online include SMS verification, account recovery via SMS, and 2-factor authentication.
This helps to combat fake accounts, spam attacks, or automated bot attacks, all while protecting users’ privacy. Platforms using zk-Phone number proofs enhance their security and give users peace of mind that their phone number will not be exposed during verification.
zk-Phone Number Proofs Features, Pros & Cons
Features:
- Verifies the ownership of a phone number.
- Based on zero-knowledge proof.
- Two-factor authentication is offered.
- Confirms human involvement.
- Privacy-preserving verification is offered.
Pros:
- Excellent protection against bots.
- No loss of number privacy.
- Significant reduction of spam and fake accounts.
- Straightforward mobile workflow integration.
- Improvement of account security.
Cons:
- Virtual numbers limit the functionality.
- Phone access is required.
- Mobile users can be blocked.
- Not all platforms will adopt it.
- SMS verification can be lost to charge.
6. zk‑Government ID Proofs
Without having to show the entire government ID, zk-Government ID proofs can verify passports and driver’s licenses. This privacy-preserving method of showing compliance with age, residency, or identity requirements is known to be zk-Identity proofing.

Signing up for regulated services, financial accounts, and accessing age-restricted content are some examples of how you can use zk-Identity to prove you’re human online. With zero-knowledge technology, platforms can confirm the legal identity of a user, combat account fraud, and ensure that human users are verified, all without exposing unnecessary personal information.
zk-Government ID Proofs Features, Pros & Cons
Features:
- Verifies a government-issued legal ID.
- Protected sensitive data via zero-knowledge proof.
- Confirms age, residency, or identity.
- Supports KYC or other regulated services.
- Prevention of fraudulent accounts.
Pros:
- Excellent anti-fraud measure.
- Protection of privacy is offered.
- Solidifies online services security.
- Supports reliable human verification.
- Ensures compliance with regulations.
Cons:
- Official ID is required.
- Casual users can be discouraged.
- Platform adoption is limited.
- Some areas do not have support for digital IDs.
- There are many complexities involved in implementing this.
7. zk‑Age Verification
Age verification services using zk-Identity privacy technology allow users to demonstrate that there are old enough to access a site without revealing their actual date of birth. Businesses can determine whether users are eligible to access age-restricted websites or services, while users’ identities remain undisclosed.

Protected access to websites such as social media, adult content, or other services requiring age verification to access, helps to safeguard minors from online predators. Additionally, zero-knowledge age verification is a solution to privacy concerns, while keeping age verification digitally compliant and safe from data breaches.
zk‑Age Verification Features, Pros & Cons
Features
- Validates age without showing date of birth.
- Based on Technology of zero knowledge proofs.
- Allows access to age restricted material.
- Method is privacy preserving.
- Undermines access for people below the required age.
Pros
- Personal data is protected.
- Compliance is made easier.
- Human verification is trustworthy.
- Easy to use shield on the internet.
- Regulatory risk is lowered.
Cons
- Might need a trusted data source.
- Platforms that use this technology will be limited.
- Cannot eliminate the existence of fake accounts.
- User verification may lead to a backlash.
- The more complex the integration the greater the risk.
8. zk‑Payment Proofs
With zk- Payment Proofs, users can demonstrate that payments have been processed in the system, without disclosing payment details, the value of the payment, or the parties to the payment. This technology is used to verify the identity of a person in the process of performing a payment transaction online.
Methods of using zk-Identity online to demonstrate that a user is a person include the access to premium services or the purchase of a product. The use of zero-knowledge payment verification technology helps to identify fraudulent actions and bot activity while ensuring privacy and providing safe user verification.
zk‑Payment Proofs Features, Pros & Cons
Features
- Confirms activity for a certain transaction.
- Zero knowledge makes the amount for the transaction private.
- Validates financial activity of a human.
- Stops illegal payment activities.
- Allows access to premium services.
Pros
- Financial privacy is preserved.
- Payment fraud is controlled.
- Human verification occurs through payment.
- Digital wallets can be used.
- Payment systems are protected.
Cons
- Payment systems will have to be integrated.
- The system cannot be used if no payment occurs.
- Adoption will be limited.
- The more complex the integration the greater the risk.
- By itself, the system will not eliminate bots.
9. zk‑Residency Proofs
With zk-Residency Proofs, users can demonstrate their country or city of residence, without disclosing their complete address. This technology helps to verify location requirements for services without compromising the user’s privacy.
Ways to use zk-Identity online to demonstrate that a user is a person include accessing location-restricted sites or services, accessing local services, or participating in local programs. Zero-knowledge residency proofs enable websites to combat fraud, fake accounts, and abuse while maintaining privacy.
zk‑Residency Proofs Features, Pros & Cons
Features
- Validates a certain country and city of residence.
- Zero knowledge technology will keep the full address private.
- Allows the use of geo-restricted access.
- Validates the use of certain services.
- Privacy preserving location technology.
Pros
- Privacy is maintained.
- Reduces creation of accounts that are fake.
- Compliance to regulation this technology is implemented.
- A small amount of data is required.
- Trustworthy human verification exists.
Cons
- Adoption will be limited.
- The data for the verification of the region may not be available.
- Cannot verify identity as a single solution.
- This technology will be implementation is platform dependent.
- The more complex the integration the greater the risk.
10. zk‑Session Activity Proofs
The zk-Session activity proofs validate that an individual is actively present on a given platform. They do not expose specific details on what activities are being performed or disclose PII (personally identifiable information).

This feature confirms that an activity or event is not a “bot” or an automated process. Multiple online events, polls or workflows can use zk-Identity to verify participation. By using zero-knowledge session proofs, online activities as an individual are often guaranteed to be secure and not automated or performed by a real person.
zk-Session Activity Proofs Features, Pros & Cons
Features:
- Proof-of-human activity in an online session.
- Privacy by Zero-Knowledge.
- Proof-of-human reduces automated bot activity.
- Proxy-activity proof supports secure workflow.
- Engaging activity is tracked, but specifics are not disclosed.
Pros:
- Effective bot detection.
- Improved privacy.
- Trust in platform is increased.
- Real-time functionality.
- Genuine users feel seamless.
Cons:
- Active sessions must be monitored.
- Complicated integrations.
- Fake users cannot be deterred by this alone.
- Underused.
- Increased burden on systems.
Conclusion
To sum up, zk-Identity provides an innovative solution to prove humanity online without sacrificing privacy. Each method, including zk-Biometric and Device Attestation proofs, as well as Email, Phone, and Government ID verification, provides authenticity verification without compromising privacy.
Using zk-Social Graphs, Age, Payment, Residency & Session Activity proofs, and Graphs, Platforms can block bots and decrease fraud to build trustable interfaces. Ultimately, zk-Identity users seamlessly prove their human presence, enabling online services to interact with real people while protecting personal information through zero-knowledge privacy-preserving methods.
FAQ
What is zk-Identity?
zk-Identity (zero-knowledge identity) is a privacy-preserving method that lets users prove certain attributes—like being human, age, or residency—without revealing sensitive personal information.
How does zk-Identity help prove I’m human online?
By using proofs such as zk-Biometric, zk-Device Attestation, or zk-Social Graphs, platforms can verify that an account belongs to a real human and not a bot, while keeping your personal data private.
Can zk-Identity verify age without revealing my birthdate?
Yes. zk-Age Verification allows platforms to confirm you meet age requirements without exposing your exact birthdate, protecting your privacy.
Is zk-Email or Phone Proof safe?
Absolutely. zk-Email Ownership and zk-Phone Number Proofs confirm you control an email or phone number without sharing the actual contact details, preventing spam or fraud.
How does zk-Identity prevent bots and fake accounts?
zk-Identity methods, including zk-Biometric Proofs, zk-Session Activity, and zk-Social Graph Proofs, ensure only verified humans interact with platforms, reducing automated attacks and fake profiles.